What You Should Know About Ransomware

By now most businesses should be aware of the very real threat that Ransomware poses. If you are not yet up on the subject, let me provide a simple definition. Ransomware is a malicious program that infects a unsuspecting victim’s computing device delivered through email, a compromised website, an infected thumb drive, or any number of various other methods. Then Ransomware targets specific files or data types of an application by its file extension. For example, Microsoft Word Document extensions are .docx. Once identified, the file is then encrypted with a asymmetrical encryption key. The key to unlock them should be kept with the malicious coder. The first step to protect against ransomware is understanding the how of it.
Statics clearly show that small businesses are not taking cyber seriously enough and they’re paying the price.
It should also be understood that over 40% of all Ransomware attacks are targeting small business. The risk factors are high for small businesses because the small business owner or employee is more likely to use a dual purpose computer for both business and personal use. They are less likely to have a properly patched and monitored firewall if one is present at all. Is likely not to be filtering email through a third party filter tool. Or worse, use a public email for personal use on the business computer (@yahoo, @hotmail, ETC). Is more likely to use a USB storage device that goes from a business to an unprotected computer. Or perhaps all of these threats are present along with some that are not listed (Yes, there’s more). With each risky use of a computer, the chance for falling victim rises.
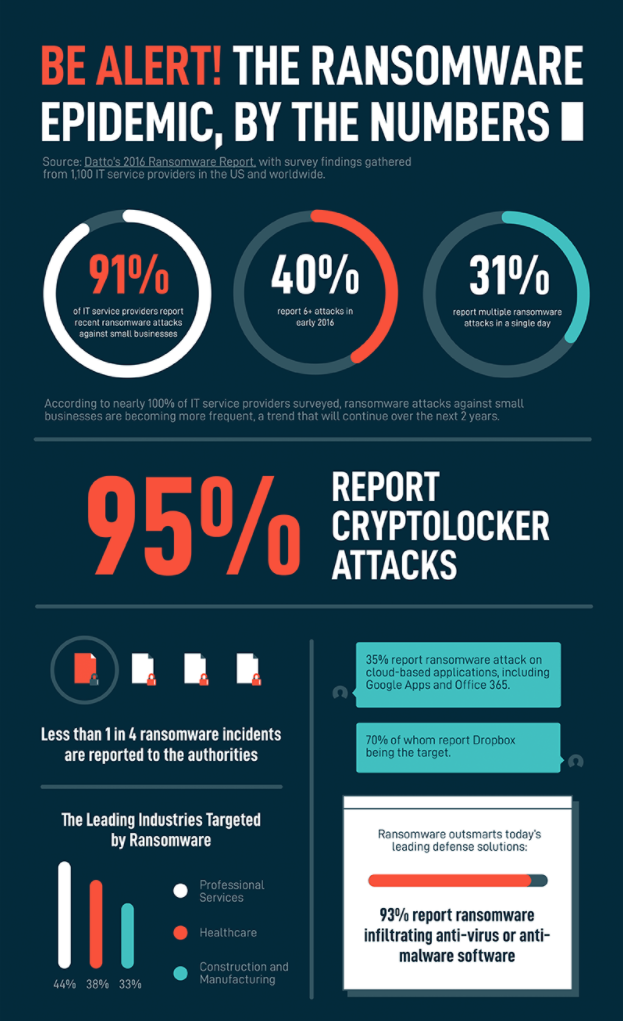
Numerous statics clearly show that small businesses are simply not taking cyber security seriously enough – and they’re paying the price. Don’t take my word for it, see what Forbes magazine has to say.
Let’s hope you are never the victim of a ransomware attack. It is definitely a nasty predicament – ask anyone who has fallen victim. But if you are attacked or better yet want to prepare yourself for an attack, consider these steps.
Don’t Pay The Ransom
Statically, only one in four victims that pay the ransom actually get a fully usable data set in exchange for the ransom that is paid. And the average ransom demanded for small businesses is averaged at $6,200!
The FBI discourages any entity from paying the ransom as this has the effect of encouraging the attacker to continue using malware to seek other potential victims.
Have Good Backups Of Critical Data
The very best way to ensure you can recover from a ransomware attack is to have a good, recent backup of all your file level and databases. In this way, you can completely wipe the infected system or systems and then restore the data from a previous day’s backup.
It is also worth mentioning here that if you have backed up the data but not performed a successful recovery of that data to a different computer than the one you backed up, you don’t have a backup – you have a wish. And a wish is not a proven way to recover from a ransomware attack! Back up the data and then have the backup tested. It should be tested every time a physical change is made to the underlying hardware platform the backups are performed against or being restored to.
Ensure Your Antivirus Includes Ransomware Protection
Not all antivirus (AV) developers are the same. While some AVs do carry anti-ransomware protection in their software package many do not. Many of the AV developers also understand that some consumers are looking for the lowest price product. So in order to stay competitive the AV developer may provide ransomware as an additional module to purchase for this protection.
In general, it is not a good idea to decide on your security product by picking the lowest priced product. Generally, if a product is priced well below or well above the market price, there is a reason for it. John Glenn is attributed with commenting on America’s space race saying, ‘I felt exactly how you would feel if you were getting ready to launch and knew you were sitting on top of 2 million parts — all built by the lowest bidder on a government contract.’ Cheaper doesn’t mean worse or better, but in general it is a good indicator of product quality.
Keep Operating Systems and Antivirus Protection Up-To-Date
Today, most Operating Systems and Antivirus developers products are self updating. That is, they will ‘phone home’, find and then install the latest updates available. However, and this is a big however, many times the update is not completed until the computing device is rebooted. You should reboot immediately after you complete the updates. Take this as an opportunity to reduce eye fatigue. You should look away from your computer screen every 15 to 20 minutes to reduce the effects of blue light on the eyes.
A reboot of your device will commit the updated packages to your device’s configuration database. In the Microsoft Windows world, this central configuration database is called the Registry.
The Best Defense Is A Good Offense
When one of my teammates or I was knocked to the turf during a football game or a scrimmage and then hobble to the sidelines a little humbled, my old high school football coach would grab you by the face mask and say, ‘If you don’t want to be hit by that player (pointing his finger at the field of play for emphasis), hit him first!’ Yeah, thanks coach! What he meant was – that just happened because you weren’t paying attention or you missed an assignment on a given play. You got caught slipping!
Don’t get caught slipping. Be proactive about the security you use to provide a living for your family and the families of the people you employ. If the data that is critical to your business is unrecoverable because of an attack, you may find your business in some pretty serious trouble!

Don’t Lose Hope
From the end user perspective, cyber security is about awareness and making good choices. Do the things you know to do and avoid risky behaviors. Trust but verify websites and email messages. And, if you’re reading this because you’ve just been compromised, go easy on yourself. It doesn’t mean you lack commonsense or somehow this was your fault. Ransomware is developed and distributed by a group of intelligent and yet unsavory thieves taking advantage of you. I would suggest that you get some help from a reliable technology professional.
If you have questions or comments be sure to leave a comment
Netvolutions Technology Group is an Independent Technology Firm located in Southern California. They are dedicated to the specific technology and security needs of the Small and Medium Size Business community.



I am very impressed.